In May 2026, as we celebrate World Quantum Day, the digital landscape faces a dual-threat paradox. On one hand, Generative AI has birthed highly sophisticated Deepfake Scams that can mimic human identity with terrifying precision. On the other, the looming shadow of Quantum Computing threatens to shatter the encryption foundations we’ve relied on for decades. If you think a simple padlock icon (HTTPS) is all you need to stay safe, you are living in the past.
1. The Rise of "Living" Deepfake Scams
The viral trend currently sweeping the United States isn't just about fake images; it’s about Real-Time Deepfake Hijacking. Scammers are now using Agentic AI to conduct live video calls, impersonating CEOs or family members to authorize multi-million dollar transfers. In this environment, Identity Verification has become the new perimeter.
Standard HTTP is a death sentence in this era, but even basic HTTPS is being challenged. We are moving towards a "Zero Trust" web where the certificate doesn't just encrypt data; it must cryptographically prove the provenance of the content to ensure it wasn't manipulated by an AI at some "man-in-the-middle" point.
2. World Quantum Day: A Warning for Encryption
The 2026 World Quantum Day highlighted a critical milestone: Harvest Now, Decrypt Later (HNDL) attacks. State actors and sophisticated hackers are currently intercepting and storing encrypted data, waiting for the "Q-Day"—the moment a fault-tolerant quantum computer can crack RSA and ECC algorithms in seconds.
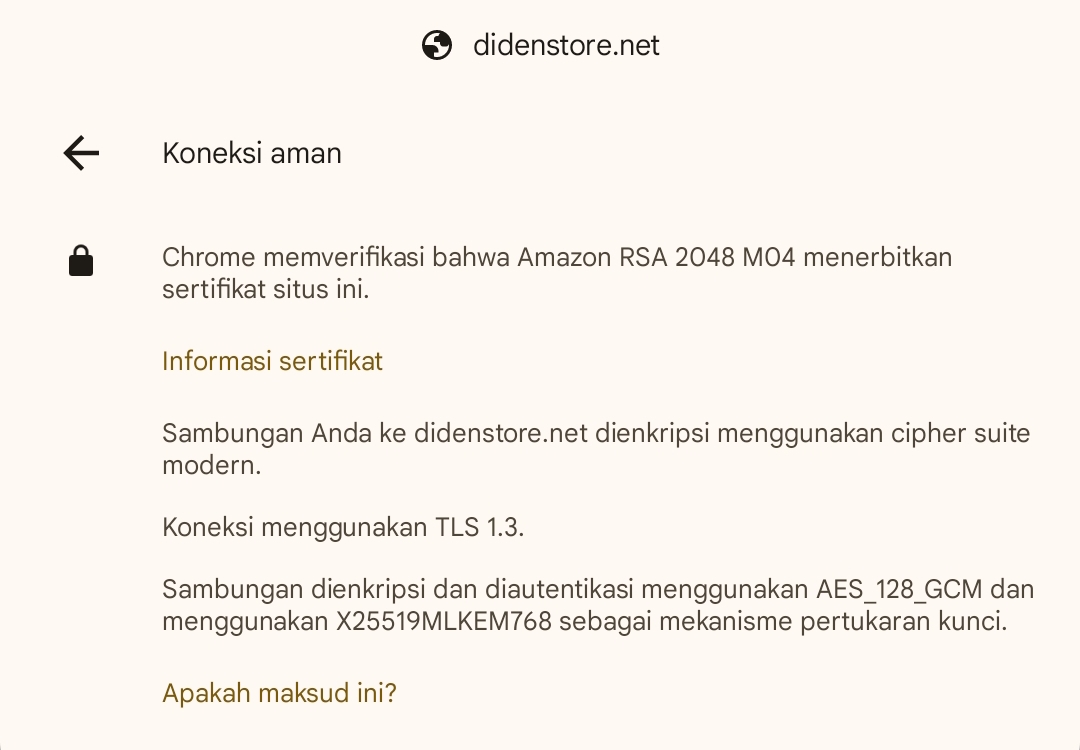
This is why leading infrastructure providers, including the ones used by Diden Store, have transitioned to Post-Quantum Cryptography (PQC). Algorithms like ML-KEM (Kyber) and ML-DSA (Dilithium) are now the standard defense against the quantum future.
3. Diagram: The Defense Architecture Against Quantum & AI Threats
Note: Modern security stacks now perform AI-based deepfake detection at the CDN Edge before the data even reaches the user's screen.
4. Implementing PQC via Global CDN Giants
Implementing quantum-grade security manually is a nightmare. This is where Multi-CDN strategies become vital. By leveraging the combined power of Cloudflare, AWS CloudFront, and Fastly, we can distribute Quantum-Resistant certificates globally.
Cloudflare’s Role in Post-Quantum Security
Cloudflare has been a pioneer in deploying Kyber (ML-KEM). By enabling the "Post-Quantum" toggle in your dashboard, you ensure that every handshake between your visitors and the Edge is resistant to quantum sniffing. This is the "Orange Cloud" magic in 2026.
AWS CloudFront & ACM PQC Integration
Amazon Web Services now allows users to issue Hybrid Post-Quantum TLS Certificates through AWS Certificate Manager (ACM). When paired with CloudFront, these certificates provide a dual layer of protection: traditional ECC for legacy devices and PQC for modern browsers.
By leveraging AWS's global edge network, your site is not just faster, but mathematically shielded against the decryption threats of the next decade.
5. Comparison: Standard HTTPS vs. Post-Quantum HTTPS
| Security Feature | Legacy HTTPS (Pre-2024) | Modern PQC-HTTPS (2026) |
|---|---|---|
| Encryption Algorithm | RSA-2048 / ECC P-256 | ML-KEM (Kyber768) |
| Quantum Resistance | None (Vulnerable to Q-Day) | Full Quantum-Resistance |
| AI Interaction | Passive Delivery | Edge AI Deepfake Filtering |
| Handshake Speed | TLS 1.2 (Slower) | TLS 1.3 + QUIC (Instant) |
6. FAQ: Navigating the New Security Norms
Q: Does Post-Quantum encryption slow down my website?
A: Surprisingly, no. While the keys are larger, the use of HTTP/3 (QUIC) and TLS 1.3 optimizes the handshake so efficiently that the latency is negligible compared to the massive security gain.
Q: How do I know if a site is "Quantum-Safe"?
A: In 2026, modern browsers like Chrome and Edge show advanced certificate details. Look for X25519MLKEM768 or similar hybrid identifiers in the security tab.
Q: Can Deepfakes be stopped by HTTPS?
A: HTTPS secures the delivery, but it doesn't guarantee the truth. However, modern HTTPS implementations include Content Provenance (like C2PA) to verify that a video or image hasn't been AI-altered.
Conclusion: Staying Ahead of the Curve
As Diden Store has always emphasized, being "online" is easy, but being "secure" is a constant battle. The combination of World Quantum Day awareness and the fight against Deepfake Scams defines our tech mission in 2026. Transitioning to a Multi-CDN, Post-Quantum architecture isn't just for tech giants anymore—it's for anyone who values digital integrity.
Disclaimer
This article is for educational and informational purposes regarding web security trends in 2026. Implementing Post-Quantum Cryptography (PQC) and AI filtering requires advanced technical knowledge. Diden Store is not responsible for any data loss or server downtime resulting from improper configuration of CDN or SSL settings. Always consult with a cybersecurity professional before making major infrastructure changes.